Hi everyone,
This is post two, responding point-by-point to the post made by Joe and the FDD team.
#1 “Why was the grant initially deactivated? → The reviewer then found further evidence!”
We honestly do not understand why MoMo making a small ~15$ to our own grant is evidence of collusion with sock puppet accounts spamming our grant since before GR15 had even started.
At the start of every Gitcoin Round MoMo makes a list of projects, funds them and shares the list on Twitter to get people to donate to them as well. The list includes Fileverse to add some visibility when he shares the list around on Twitter. Is this evidence of malicious behaviour? Clearly not.
Now, a counterpoint: you explain that MoMo donated at the same time as one of the sybil attackers gitcoin[.]co/cici0910
In fact, Tx made by MoMo was at 9:14
Tx made by cici0910 was at 9:46
Correct timestamp: docs[.]google[.]com/document/d/18dpqNdFv1dOYQpDwrOlbKePzRokawXoUsIC11BMLWbg/edit
ALSO, if you look at cici0910 account you will notice that it has been spam donating to our grant almost everyday for FOUR WEEKS.
To summarize, you suggest that MoMo making a donation at the the beginning of GR15 and that donation being done 30 minutes prior to a sybil account donation that day is evidence of a relationship. You also do not mention the fact that this account has been donating almost every day for the past 4 weeks (!!). Instead you just claim that one of those 4 weeks of donations is evidence of a relationship between us and them. We say it is a grave mistake which may be due to the reviewer not having had the time to look at the history of behaviour of that clearly fraudulent account. We sincerely hope you can consider the new evidence we just presented.
#2 “Was the proper process followed and what was the result? → This evidence included that described above plus the fact that these sybil accounts only donated to Fileverse. In the past, we have seen airdrop farming accounts normally donate to 5-10 if not more grants which are likely to have an airdrop in the future.”
When our grant was deactivated and we were informed that our grant was getting sybil attacked, there had been ~30 donors to our grant. We looked at the donations to understand which accounts were exhibiting this behavior. We found that cici0910 and wanghaha02 and wanghaha03 had been spamming ONLY to our grant for weeks, way before GR15 started. You also point out in your analysis that they all belong to the same IP, if I understood correctly.
These are clearly malicious actors that have targeted us. Are there more such accounts that ONLY donated to us or only those listed above? We ask because after the grant was reactivated we were on high alert and started looking at the profiles of our contributors. We found some odd accounts that, like you say, donate small amounts to us + 5 to 10 other grants and seem to be farming airdrops. But in those cases we are not the only target, it is a widespread issue. So going back to my question, are there more than just the three aforementioned accounts that have been donating ONLY to us? If so, could you please list them so we can help you find some connection between them and absolve us once and for all from suspicion?
Regarding more general farming accounts that donate to us AND others, we would also like to point out that a famous Crypto Twitter account by the name of @Olimpiocrypto posted a thread (twitter[.]com/OlimpioCrypto/status/1568728742494875648) on projects currently with a grant on Gitcoin, that might have an airdrop in the future. The post went super viral by crypto standards (1626 likes and 559 retweets) and probably is the reason there was an explosion of new donations after our grant was reactivated. Note also that we never mentioned doing an airdrop in the history of our project, anywhere, not on our grants (GR13-15), nor on Twitter.
#3: “It is common for a grant to post updates, but there is no way for Gitcoin reviewers or donors to know if they are honest without checking the Github. In this case, the reviewer saw a lack of activity and decided that the best bet for protecting the community was to deactivate the grant. This was a decision made in combination with all the above evidence.”
This point made by the reviewer in the initial justification (www[.]notion[.]so/https-gitcoin-co-grants-4846-fileverseio-file-sharing-between-blockchain-addre-9d967e46b920418c9367d3fbac88bce6) for deactivating our grant is that we have provided “no updates on their progress”.
This is easily disproved and we hope you can acknowledge the below evidence.
Since GR13, when we started our project, we have provided a roadmap with multiple bullet points of what we aim to achieve with the funds. GR13 allowed us to ship our Beta and keep it free ever since. On GR14 we provided a comprehensive, point-by-point update on every one of the 10+ bullet points on the roadmap that was presented in GR13. The progress was huge. The beta DApp looked completely different from what it did just after GR13 and came with many new features. Again, all free.
We also provided an updated roadmap “looking forward” to GR15. Then a few days before GR15, we updated our grant description to provide a new update on the roadmap and point-by-point summary of progress - you can see it on our result of grant 14 section of grant page: gitcoin[.]co/grants/4846/fileverseio-file-sharing-between-blockchain-addre.
The reviewer could have gone to our actual DApp and seen the progress that has happened since the previous grant round. Assuming someone actually has looked at our DApp. The progress, as we explain in the description, was quite significant.
All this continuous progress is also viewable on github[.]com/fileverse
For the brief period of inactivity on the backend repo: it is due to the fact that most of what we had promised in GR14 was achieved and pushed to prod. We are working on Fileverse Co-op / Subdomain for some time now which will be open source once it’s in proper shape and form. For verification and transparency purposes we are willing to add anyone from your team to our github organization so that you can see what work has been going on behind the scenes and that the work is in advanced state on Fileverse subdomain / co-op. This should relieve you of your suspicions once and for all.
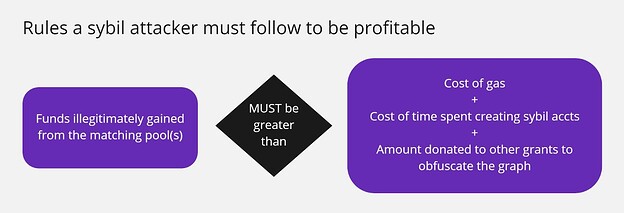
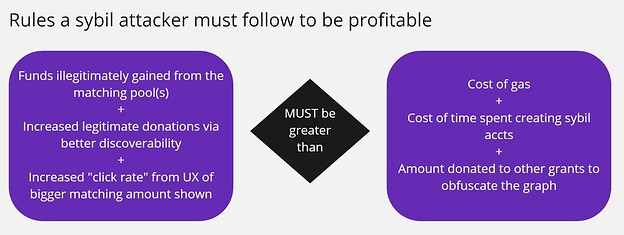
#4 What were the findings of the follow up investigation? → The behavior that has been identified is likely a newly identified attack vector which allows the attacker a “free shot” at the attack. We believe that the sybil attack is NOT an anomaly and IS a direct attack on the matching funding available. → The issue here is that Fileverse may have exploited a unique sybil attack method previously not seen by FDD. The attack skews the normal profitability equation for a sybil attack by taking advantage of the gitcoin discoverability formula and a greater user incentive created by the early donations showing donors that the matching available for their donation is much more than if they were to donate to an alternative grant.
This is an even more difficult point to accept by any reasonable measure. Before I start explaining why it is flawed and logically fallacious, allow me to repeat that, I mean no offense to the individuals that came up with the above hypothesis. I am not attacking their abilities or intelligence. However, because they are using these to accuse our project and team of being the evil masterminds behind sybil attacks, I need to be clear about the problems in their current reasoning and conclusions.
The “Free Shot Attack” you describe is a clear description of a possible type of attack on the Gitcoin platform’s algorithms:
Bad actor uses sybil attack → hope to either not get caught or get caught and not be punished → get caught and get away with it (big “if” for the attacker) → still benefit from the artificial popularity that the non-sanctioned attack granted them → makes more money from the matching than lost in doing the attack.
This makes sense.
What is deeply flawed and unjust is that this theory emerged and was linked to us (worse even, it was used to describe us) based on an assumption which itself was based on another assumption. In other words, because the end theory (of the attack vector) makes sense, you have decided to validate the antecedent assumptions that led to the theory. This is not the way you construct an argument, not one that would be accepted in court at least. Why? Because the departing assumption is not substantiated by valid evidence. Start any argument with an arbitrary assumption, and that argument will be valid insofar as the first assumption is accepted and not challenged.
Allow me to explain further.
The first assumption you make is that we are the originators of the sybil accounts. This assumption is vicious in effect because it disregards the presumption of innocence on the basis that events that are completely beyond our control have created an inevitable connection between us and malicious actors. The victims are by definition the closest entity to the attackers.
Then you add a another assumption, that, assuming the first is right, the second assumption states that we would have anticipated our sybil attack to “successfully fail” and place us in this sweet spot where our grant is reapproved and the gamble we took to make our grant super popular at the risk of killing the project, is rewarded by the lack of sanction and the gain in artificial popularity on the platform.
The problem is that this second assumption only exists as a patch, a fix to the first, flawed assumption. You saw that we were outraged by the accusation and we provided arguments to disprove it and reverse the sanction, and because we were successful and the sanction was reversed you decided to add a second assumption that our defence “was actually part of the plan all along”. That second assumption exists solely because our response was made. In other words, we can continue this game forever, where even our current post on this forum can then be used to “substantiate” a new, third assumption about how we expected this issue to escalate to the forum and planned to make a big fuss in the community and THUS gain even more donations and visibility! It never ends. That is why it’s fallacious.
That is akin to saying:
Your partner died due to a truck hitting your car → I discovered the “evidence” that you had a married couple’s life insurance → I assume that it is you who arranged for the truck to hit your car → because if you were lucky enough to survive the crash and only your partner died in it → you would gain an immense amount of insurance money which would far exceed the cost of your car and starting your life anew with another partner → the risk/reward could make sense so I conclude that my original assumption that you arranged for the crash to happen is correct.
Another way of explaining why you are wrong in creating this vile connection between our intentions and the inevitable plight that we were victims of is by using a counterfactual. Or the opposite assumption if you will. One that you haven’t even shown us the courtesy of entertaining in this post: that we are honest people busting our asses to build a useful public good.
So, let’s reverse your assumption for a second and see how the arguments develop from that reverse assumption - based on the presumption of innocence:
You discover that our grant is targeted by sybil attackers → you assume that we are innocent, honest people that were victims of their own success and fell on the radar of malicious actors (farmers or competitors, NOT inimaginable in the crypto space…) → you defend the assumption that we are innocent based on the fact that even a project with the best intentions is technologically incapable of stopping outside people from conducting these targeted attacks. The way blockchains work, it is impossible to stop a bad actor from sending you Tornado Cash dust to your account or spammy donations, for example → also you don’t find a clear link between the grantee and these multiple old and new sybil attacks, the only thing you are certain of is that attacks are happening and Fileverse is a juicy target to attackers → So you rightly decide that the burden of proof should not be on those good actors, because, by any stretch of imagination, there was nothing they could have possibly done to prevent attackers from targeting them → You decide to come up with ways to attack the attackers, and work on a better sybil resistance technique with the victims so that you can learn from their experience and prevent future injustices and the common pool from being drained from deserving public goods.
Instead, you publicly stripped us from the presumption of innocence that we deserve and presented arguments based on text book logical fallacies.
To conclude, the biggest problem I have with your argument is: what happens after Fileverse? Ok today you banish the favorite victim of a group of malicious attackers, but what happens when inevitably there is another Fileverse-type victim? You banish that victim as well for not being able to prove their innocence. And then, with the next favorite victim of malicious actors? Well you banish them as well, and so on, forever, hoping the attacks stop at some point if you remove enough juicy victims. All that because you decided to not take care of the attacker but instead to focus your attention on the closest sanctionable entity (which happens to be the victim) for being preferred by the malicious actor. GG WP, until next time.
#5 What should happen to the grant considering the evidence? →
#5.1: Nearly 70% of previous donations have been from sybil accounts → Without seeing the new equation, there was no alarm to look into this
Do you have this analysis for all the grants per round, please? This metric tells a completely different story when it is compared with other successful grants.
We are one of the top grants for the past two rounds, we started in GR13. If you take that fact alone it would explain this data. If we were a bottom 100 project in those past rounds this would indeed be a problem.
What you are essentially saying is that a top project is a good proxy indicator for the percentage of sybil accounts and/or airdrop farming activity since they are getting the bulk of all donations.
Note that during GR13 we got ~43% of ALL donations made on the platform during that round.
#5.2: The second highest percentage of sybil donors in past rounds even without being a likely future airdrop grant
Yes, and? We are to be stripped of our legitimacy in public because we are victims of our own success? Why is this evidence of our intentions exactly?
Is it our fault that we are not doing an airdrop or are you saying that we are not doing an airdrop to keep the gitcoin farm spirit alive?
Again, we are one of the top grants for the past two rounds, we started in GR13. If you take that fact alone it would explain this data. If we were a bottom 100 project in those past rounds this would indeed be a problem. What you are essentially saying is that a top project is a good proxy indicator for the percentage of sybil accounts and/or airdrop farming activity since they are getting the bulk of all donations.
Can you put a similar analysis for all the famous grants per round? So we see how our “second highest percentage” compares with others in the, say, top 30 projects.
Also, we would also like to point out again that a famous Crypto Twitter account by the name of @Olimpiocrypto posted a thread (twitter[.]com/OlimpioCrypto/status/1568728742494875648) on projects currently with a grant on Gitcoin, that might have an airdrop in the future. The post went super viral by crypto standards (1626 likes and 559 retweets) and probably is the reason there was an explosion of new donations after our grant was reactivated. This happens a lot and affects every point you make in this list. What it should not affect is the presumption of innocence.
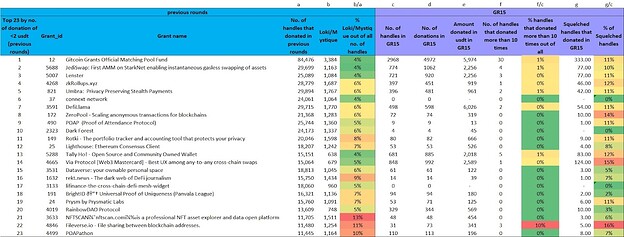
#5.3: Over 10% of handles that donated during GR15 donated over 10 times during → This is the highest percentage by far!
Apologies, but this is a statistics 101 mistake you made to support your point. Let me explain why:
You are making a percentage based comparison without mentioning the difference in absolute numbers. Thank you for sharing the sheet though, this helps in building a constructive feedback.
While computing the stats you use to claim “highest percentage by far!” we only had 31 contributors + 71 donations, so you got this statistic. The other projects on your sheet, which you are using to make a comparison that makes us look bad, have a much higher number of contributions. JediSwap, Umbra, Tally-ho, and the matching pool fund are the other victims of the same targeting we were, which you use to say “highest percentage by far”. So let’s compare properly to see why your statistic is misleading:
- JediSwap had a higher number of contributors to us by a factor of 25!!
- Umbra had a higher number of contributors to us by a factor of 13!
- Tally-Ho had a higher number of contributors to us by a factor of 21!
- Gitcoin matching pool had a higher number of contributors to us by a factor of 95!
And yet, you decided that our 31 contributors were enough data points to determine a percentage that is a) Sufficient indication of fraud and b) Appropriate to compare with other projects that had at a minimum over 13 times the amount of contributors.
Since when do statisticians only take the percentage without mentioning the absolute number to give context? How is that percentage relevant to an absolute number of 31 contributors when the projects compared to it have hundreds more contributors diluting the relative percentage?
I’ll give the benefit of the doubt to the person who ran those numbers, but I insist that you correct the record please.
#5.4: Over 16% of past donations came from Squelched users → This is THE MOST PAST SYBIL DONATIONS of any grant in GR15
This is the same issue as the above point. It’s a point that stands only because you don’t mention the absolute number.
This is based on the first hours of our GR15 where Filverse had less than ~70 donations in total and 31 contributors. If you replicate this now, is the number 16%? How much smaller is it? This is important for a statistical analysis that will negatively impact our whole project.
This argument is basically implying that to kill any grant on Gitcoin from now on, one malicious actor only needs to reach a 16% or higher by making a super obvious sybil attack very early on on a grant. In other words:
I hate project Y → within the first 2 hours of GR16 I make sure I attack it with enough very obvious sybil accounts → because its the first 2 hours the project doesn’t have many donations yet so my sybil accounts become a big percentage of the total contributors and donations → that project grant is deactivated → GG, easiest attack vector ever for competitors and malicious actors looking to kill a project.
#5.5: Fileverse is in 22nd place for most donations under $2 when looking at all active grants previous donations
To repeat, please note that during GR13 we got ~43% of ALL donations made on the platform during that round. During the post GR13 assessment live on youtube, you mentioned that we were in the top 5 projects if there was no cap on matching. Why are you surprised that a top project is a good statistical proxy to the highest amount of sybil donations and/or airdrop farming activity?
We have built something useful here, that also is free and open source. That anyone with or without blockchain experience can use. That is non-financial/speculative and appeals to a different, less money oriented crowd. So you are saying it’s bad to be popular? Or is it bad that people like our product / grant? Is it bad that Bernie Sanders got the most amount of low donations in the history of the USA elections by a huge margin because he was appealing to a different class of new voters?
One final, super important point, that relates to this and every point you make above.
What you are facing here, and failing to acknowledge despite the harm and distress you are causing us, is a chicken and egg problem:
What came first, the grant’s success or the sybil? Is the sybil there because of the success of the grant or is the success there because of the sybil?
The grant’s early success is because of the nature of our free DApp, because it’s easy to use by anyone and requires no money, because it replicates in the web3 world one of the most popular activities on the web (file sharing), because of a smiley, shiny logo and because of the twitter grind of its founders. Additionally, GitcoinDAO is not the only group that has done due diligence on us, every funder that received our Ecosystem and Cause Round Eligibility Application and decided to add us to our side-round, namely, ENS, Polygon, a16z, and Web3Social, saw that we are a serious, deserving public good.
Because of that early success, our grant became the perfect target. Sybil attackers came flocking to us like vultures on a carcass, and did so so strongly and early that you are not capable of distinguishing our success from their manipulations. And you decide, with no evidence, that the sybil came first, that we are at fault, that we are taking the risk to kill our own project, a public good we have been working on with passion since day one, that by any measure is useful to a lot of people, in order to maybe gain the benefit of a bit of grant matching money.
If we were half the evil geniuses you describe, I can assure you there would be better ways for us to make money in crypto. We would already have a token by now, we would have already rugged, we would be like so many other crypto scammers that made it by exploiting people’s greed. Not building a self-evident, working, free, open source, DApp that keeps improving every day.
#5.6: There are 4 more items which are available for steward council review if requested
Please share them in public as well. Would like this to be transparent to the community and since you are painting us as malicious actors.
The only way to fight this injustice, beyond having 3 founders drafting these answers instead of working on the product, is to openly invite all accounts we admire, or think are relevant for the situation you are putting us in, to invoke their knowledge and experience and help us solve this.
Fileverse team
![]()